The ByBit Heist: A Turning Point in Cybercrime
One single event defined the cryptocurrency crime landscape in 2025: the attack on the ByBit exchange. On February 21, 2025, North Korean hackers executed a breach that the FBI dubbed "TraderTraitor," resulting in the theft of roughly $1.5 billion in virtual assets. This isn't just another exchange hack; it is the largest cryptocurrency theft in history, accounting for nearly 69% of all funds stolen from crypto services this year. What makes the ByBit attack truly terrifying is the target. The hackers managed to compromise a cold storage wallet, a hardware wallet kept isolated from online networks to prevent remote attacks. For years, cold storage was the gold standard of security, considered virtually impervious to outside breach. The fact that the DPRK could crack this infrastructure suggests a massive leap in their technical capabilities or a dangerous level of cooperation with underground financial networks, particularly in China, to facilitate the breach and the subsequent movement of funds.How the DPRK Evades Sanctions Through Digital Assets
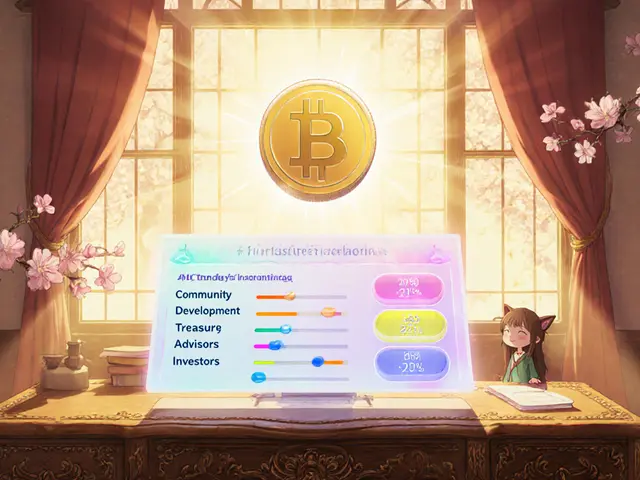
North Korea doesn't just steal; it launders and infiltrates. The regime uses a three-pronged approach to turn stolen code into hard currency while dodging international sanctions. First, they utilize complex laundering hubs in third countries. Cambodia has become a primary center for these activities due to its loose financial and gambling regulations. A prime example is the Huione Group, a Cambodia-based financial entity designated as a primary money laundering concern by the U.S. government. Between 2021 and 2025, roughly $37.6 million in North Korean-linked crypto flowed through Huione. By using subsidiaries like Huione Crypto to issue stablecoins that cannot be frozen, the regime can bypass global regulations and convert illicit gains into legitimate assets without a trace. Second, the regime employs a "sleeper cell" strategy with IT workers. The United Nations estimates that North Korean developers working abroad generate up to $600 million annually. These workers don't put "Pyongyang" on their resumes. Instead, they use fake identities, posing as nationals from Russia, China, or various African and Southeast Asian nations. They use VPNs and remote management software to pretend they are based in Europe or the U.S. Many Western tech firms have unknowingly hired these developers, who then use their inside access to plant backdoors or conduct social engineering attacks on their employers. Third, they leverage high-speed conversion. Once a hit like TraderTraitor happens, the assets are immediately split across thousands of addresses on multiple blockchains. This fragmentation makes it incredibly difficult for blockchain analytics firms to track the full trail before the assets are swapped for fiat currency in unregulated markets.| Method | Estimated Scale/Impact | Primary Tactic |
|---|---|---|
| Direct Exchange Hacks | $2.17B+ (2025 YTD) | Cold storage breaches & Social Engineering |
| Freelance IT Workers | ~$600M annually | Identity theft & remote employment fraud |
| Laundering Hubs | Millions via Cambodia | Unfreezable stablecoins & gambling sectors |
The International Response and Enforcement
The U.S. government has shifted from passive monitoring to aggressive disruption. The Office of Foreign Assets Control (OFAC), a financial intelligence unit of the U.S. Department of the Treasury that enforces economic and trade sanctions, recently sanctioned the Korea Sobaeksu Trading Company. This front company was used to procure materials and generate clandestine revenue, including through the fraudulent IT worker schemes mentioned earlier. Key individuals like Jo Kyong Hun, a Sobaeksu IT team leader, have been identified as the bridge between the technical hacking teams and the financial operations. The U.S. Department of Justice has even unsealed indictments against North Korean nationals for sanctions avoidance, with reward offers for their capture ranging from $500,000 up to $7 million. However, the political pressure is mounting. U.S. Senators Elizabeth Warren and Jack Reed have pushed the Treasury and DOJ to redouble their efforts, arguing that the ByBit hack proves that traditional sanctions are no longer enough. The core problem is that as long as there are bridges between decentralized finance (DeFi) and the traditional banking system, North Korea will find a gap to crawl through.
The Future of Defense in a State-Sponsored Threat Era
If a state-sponsored actor can breach a cold wallet, what is actually safe? The FBI is now urging the private sector to take a more active role. They are calling on RPC node operators, blockchain analytics firms, and DeFi services to proactively block any transactions associated with the TraderTraitor addresses. For cryptocurrency exchanges, the lesson is clear: the cost of security must go up. Simple two-factor authentication and standard firewalls aren't enough when you're fighting a national intelligence agency. We are seeing a shift toward multi-party computation (MPC) and more rigorous identity verification for employees who have access to critical infrastructure. The reality is that North Korea has fundamentally changed the risk profile of the crypto industry. They aren't just hobbyist hackers in a basement; they are a disciplined military operation with an unlimited timeline and a desperate need for cash. The battle for the blockchain is no longer just about code-it's about geopolitical warfare.Why does North Korea ban crypto for citizens but use it for the state?
The ban prevents the general population from accessing foreign currencies or decentralized financial systems that could undermine the regime's total control over the economy. By monopolizing crypto access, the state can use the technology's anonymity to bypass sanctions and fund military programs without allowing the public to gain financial independence.
How did the ByBit hack happen if the funds were in cold storage?
While the exact technical details are often kept secret, evidence suggests a combination of advanced social engineering and the compromise of IT personnel. By infiltrating the humans who manage the hardware, attackers can either trick the system into signing a malicious transaction or gain physical/remote access to the keys through compromised management software.
How do North Korean IT workers hide their identity?
They typically use stolen or fake identities from countries like China or Russia. They use VPNs to mask their IP addresses, making it appear as if they are working from a US or European city, and often use remote monitoring tools to maintain the illusion of being local developers.
What is the role of Cambodia in these operations?
Cambodia provides a loosely regulated environment where companies like the Huione Group can operate. These entities act as bridges, taking stolen cryptocurrency and moving it through gambling sites or issuing unfreezable stablecoins to wash the funds before they enter the global banking system.
Can individual users be affected by these state-sponsored hacks?
Yes. While the primary targets are large exchanges like ByBit, the secondary effects include increased volatility in the assets the hackers dump on the market and the potential for the "bridge" services and DeFi protocols they use to be compromised, putting other users' funds at risk.







Write a comment
Your email address will be restricted to us